Demo Video
MITRE Att&ck Matrix & Elisity with Elisity: A Guide to Identity-based Microsegmentation
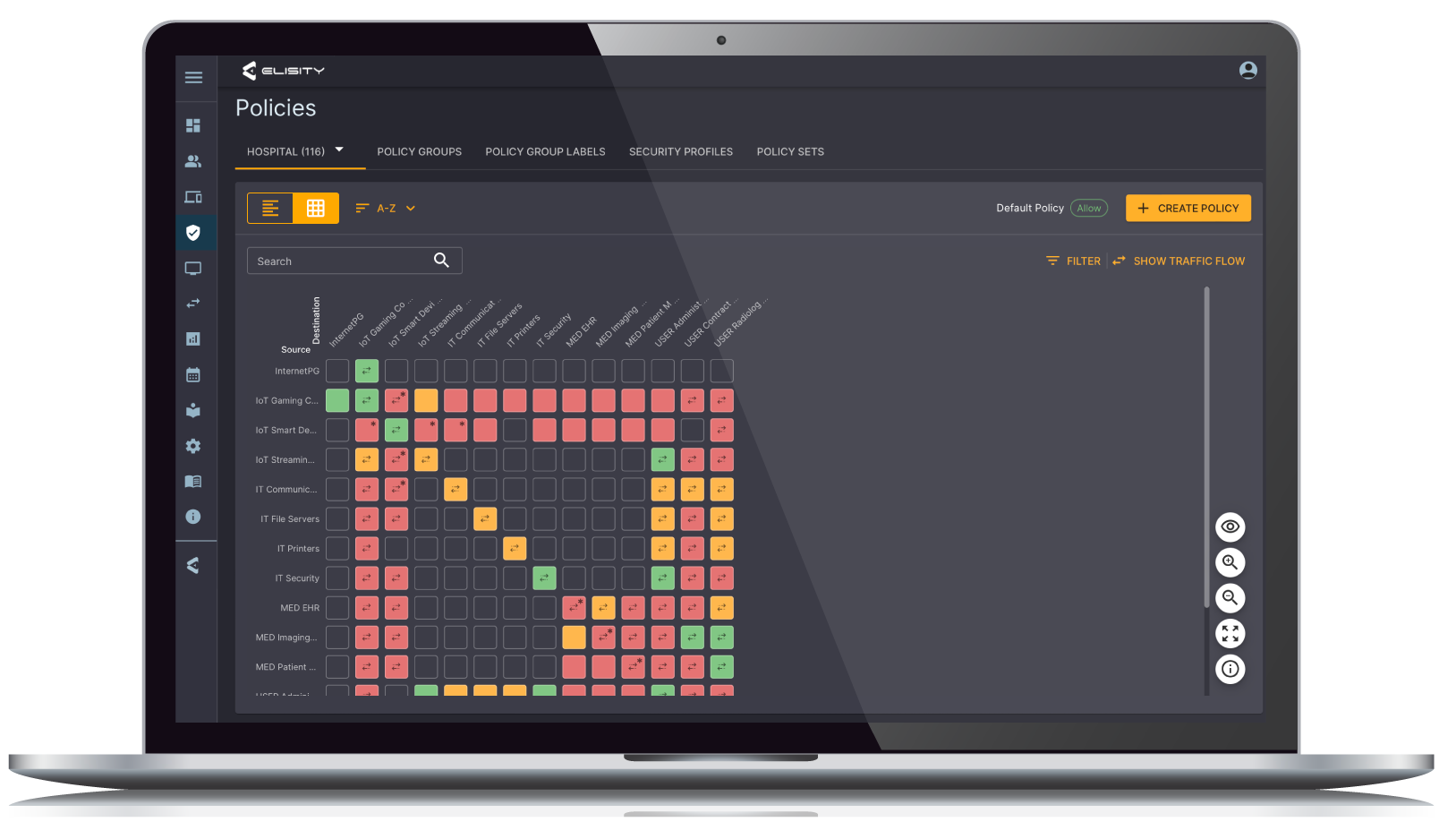
Join us as we delve into the MITRE attack matrix and demonstrate the efficiency of identity-based micro-segmentation in securing IT and OT networks. Learn how Elisity's innovative solutions simplify the mitigation of cyber vulnerabilities.
Ready to get started?
Secure Your Network Now
Don't let threats take you by surprise. Reclaim control of your network's security posture with Elisity. Unlock enhanced threat detection and policy management capabilities to achieve cybersecurity objectives confidently.

.png)

