Elisity Palo Alto Networks Panorama Integration: Automated Firewall Policies
Elisity + Palo Alto Networks Panorama™: Eliminate manual firewall address group management with automated Dynamic Address Groups. Transform firewall policy enforcement with identity-based asset classification and seamless Panorama integration.
-
Demo
Automating Palo Alto Networks Dynamic Address Groups with Real-Time Device Intelligence
Watch Elisity product managers demonstrate seamless Palo Alto Networks Panorama integration, real-time policy group mapping to DAGs, and automated device classification that eliminates manual firewall address group maintenance. See live quarantine workflows and IoT Security enrichment in action.
Support Documentation
Palo Alto Networks Firewall Integration
Policy Group Derived Dynamic Address Groups (DAG)
Palo Alto Networks Panorama Integration
Policy Group Derived Dynamic Address Groups (DAG)
Challenge
Manual Firewall Address Group Maintenance
Security teams spend countless hours manually tracking and updating firewall address groups as new devices join the network, creating operational bottlenecks and increasing the risk of misconfigurations. Traditional firewall management requires administrators to continuously classify assets and maintain static IP-based policies, forcing valuable security resources to focus on administrative tasks rather than strategic policy development and threat response.

Elisity Solution
Automated Asset Classification and Dynamic Address Group Management
Elisity eliminates manual firewall administration by automatically discovering and classifying all campus-connected assets within the Elisity-secured architecture, then dynamically assigning devices to Policy Groups that seamlessly propagate to Palo Alto Networks firewalls as Dynamic Address Groups (DAGs). This automated approach removes the operational burden of manually maintaining address groups while ensuring firewall policies always reflect real-time network conditions and device identities.
Challenge
Static Device Classification Creates Security Gaps
IP-based firewall policies fail to reflect real-time changes in device identity, role, or risk level, creating blind spots in security enforcement across multiple sites and network segments. Without automated device classification and dynamic address group updates, organizations struggle to maintain consistent security postures while devices move between network locations or change their operational status.

Elisity Solution
Identity-Based Policy Enforcement with Real-Time Classification
The integration leverages Elisity’s IdentityGraph™ to provide granular device context—including device type, location, and trusted status—that enables dynamic, risk-aware firewall policy enforcement rather than static IP-based rules. Security teams gain precise control over network access by using policies that reference Dynamic Address Groups automatically populated based on real-time device identity and behavior—enabling least-privilege access without the complexity of manual firewall management.
Challenge
Scaling Firewall Management Across Enterprise Networks
As organizations grow their IT, IoT, OT, and IoMT environments, manual firewall policy management becomes unsustainable, leading to policy drift, security gaps, and compliance violations. Enterprise security teams need automated solutions that can discover, classify, and segment thousands of devices without requiring constant manual intervention or complex policy rewrites.

Elisity Solution
Seamless Enterprise Integration with Zero Disruption
Deploy comprehensive firewall automation across your entire Palo Alto Networks environment through API integration with existing firewalls or Panorama—no network re-architecting required. The solution unifies device-group assignments across platforms with Elisity's multi-vendor approach, ensuring OT, IoT, IoMT, and IT devices are categorized consistently while maintaining operational continuity and leveraging your existing security infrastructure investments.

Resources
Download the Elisity + Palo Alto Networks Integration Brief
Expanding the Scope of Identity-Based Security and Bringing Access Layer Visibility to the Network Boundary
Explore Our Integrations
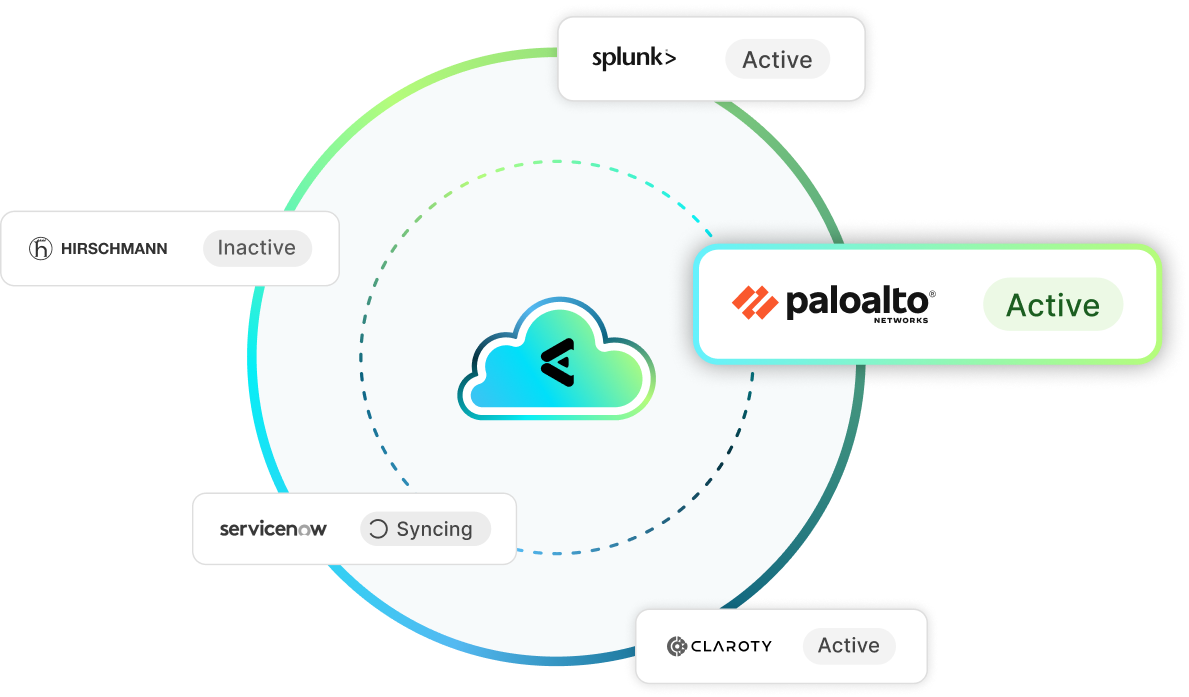
Elisity activates least privilege access by harnessing the tools you already trust. With deep API integrations and real-time data correlation, your existing stack becomes a powerful engine for intelligent, identity-aware policy enforcement.
Device Intelligence / Risk Status
EDR / Risk Status
CMDB
Network Enforcement Point
User Identity / Device Metadata
SIEM
Palo Alto Networks + Elisity Integration FAQ
Get answers to common questions about how Elisity integrates with Palo Alto Networks to automate Dynamic Address Groups and simplify firewall policy management.
Elisity IdentityGraph discovers and classifies every device on your network, then maps them into Policy Groups. These Policy Groups are automatically pushed to Palo Alto Networks firewalls as Dynamic Address Groups (DAGs) through a direct API integration. As devices join, move, or change status, DAGs update in real time, keeping firewall policies aligned with actual network conditions. The integration supports both direct firewall connections and Panorama for centralized management.
Dynamic Address Groups allow Palo Alto Networks firewall rules to reference auto-updating groups of IP addresses rather than static lists. Elisity populates these DAGs from IdentityGraph device classifications, eliminating manual maintenance of address groups across IT, IoT, OT, and IoMT device types. This means firewall policies stay accurate as your network changes, without requiring administrators to manually track and update device assignments.
No hardware changes are required. The integration connects through the Palo Alto Networks API to your existing firewalls or Panorama deployment. You can deploy in minutes and start with a subset of Policy Groups to validate before expanding. Elisity works alongside your current firewall configuration without requiring network re-architecture or VLAN reconfiguration.
Yes. Elisity uses agentless device classification through IdentityGraph, combined with enrichment from device intelligence partners like Claroty, Armis, and Nozomi Networks. Unmanaged IoT and OT devices are automatically classified and mapped to the appropriate Policy Groups, which then propagate to Palo Alto Networks DAGs for identity-aware firewall enforcement without requiring agents on any endpoint.
Manual address group management leads to 70-80% rule bloat as security teams struggle to keep pace with device changes. Elisity syncs device identity to DAGs in real time: new devices are classified in seconds and DAGs update automatically. This eliminates the operational burden of tracking IP addresses, reduces misconfigurations from stale rules, and lets security teams focus on policy strategy rather than administrative maintenance.
Resources

How to Automate Palo Alto Networks Dynamic Address Groups with Identity-Based Classification

Modern vs. Legacy Microsegmentation: The Evolution of a Critical Zero Trust Requirement


.png)




