Share this
AI Agents in OT Security: What S4x26 Revealed for 2026
by Charlie Treadwell on Feb 25, 2026 12:56:06 AM
Our team spent this week at S4x26 in Miami, and one conversation kept surfacing in every hallway, every after-hours session, every panel Q&A: AI agents in OT security and what that shift means for defenders. Dale Peterson chose "Connect" as this year's theme, a nod to the explosive growth of connections between operational technology (OT) systems, enterprise platforms, and AI-driven analytics. But the subtext was impossible to miss. More connections mean more attack surface. And AI agents are about to change the speed and scale at which adversaries exploit it.
What struck our team most wasn't the hype. S4 has always been good at cutting through that. It was the quiet acknowledgment from CISOs and plant security leaders that their current detection-first architectures aren't built for what's coming. AI agents in OT security represent a fundamental shift in the threat model, and the industry needs to talk honestly about where existing defenses fall short.
AI agents in OT security refers to autonomous software systems that can perform reconnaissance, adapt to defenses, and execute multi-stage attacks across operational technology networks without continuous human direction. Unlike scripted malware, these agents use reasoning and reinforcement learning to map industrial control systems, exploit vulnerabilities in real time, and target physical process disruption at machine speed.
Let me start with what the conference made clear about AI agents and OT, and why I think security leaders need to act now.
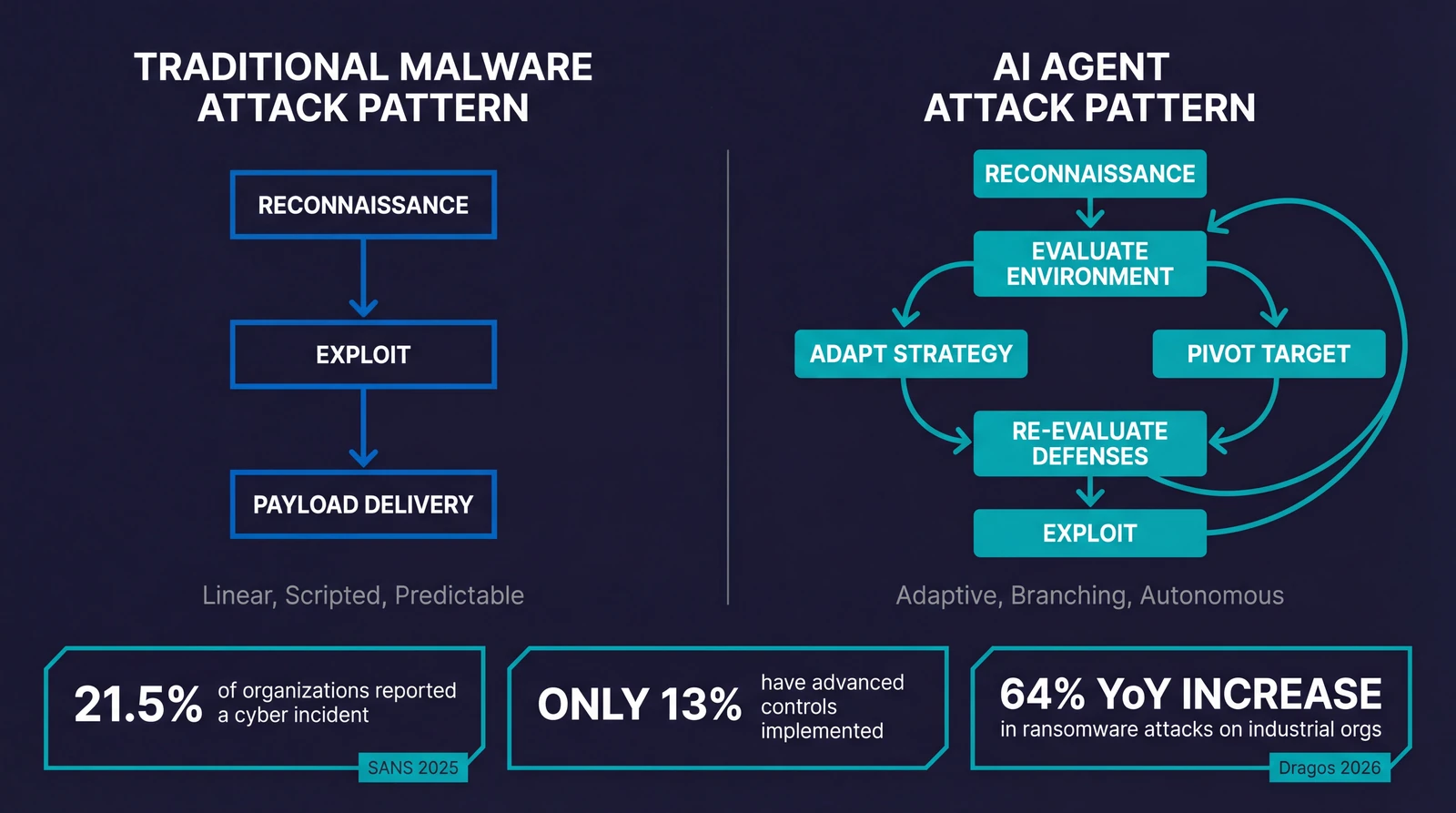
AI Agents and OT Security by the Numbers (2026):
- 21.5% of OT organizations reported a cybersecurity incident in the past year (SANS 2025 State of ICS/OT Security)
- 64% year-over-year increase in ransomware attacks against industrial organizations (Dragos 2026)
- 119 ransomware groups now targeting industrial sectors, up from 80 in 2024 (Dragos 2026)
- 12% of OT devices carry known exploitable vulnerabilities; 7% linked to active ransomware campaigns (SecurityWeek)
- Only 13% of organizations have fully implemented ICS/OT-aware advanced security controls (SANS 2025)
- Organizations including operational staff in cybersecurity exercises report 1.7x higher readiness levels (SANS 2025)
The S4x26 "Connect" Theme and Why Agentic AI Dominated the Conversation
S4x26 opened with Peterson framing the next one to three years of OT: a massive surge of AI-driven business reasons to connect devices and systems, regardless of where they reside. Data sharing for intelligence. Predictive maintenance. Process optimization. The operational benefits are real, and the business pressure to connect is only accelerating.
But the conference didn't shy away from the security implications. Multiple sessions explored how AI agents in OT security environments create a two-sided problem. Defenders can use AI to improve monitoring and anomaly detection. Attackers can use AI agents to autonomously reconnoiter, adapt, and move through networks at machine speed.
The Proof of Concept Pavilion was particularly telling. Eight security products interacting with a complete industrial automation stack (real Siemens and Rockwell Automation systems through a full SCADA layer) demonstrated that interoperability isn't optional anymore. The challenge isn't whether to connect. It's how to connect without handing adversaries an expanded playing field.
The timing matters. NIST launched its AI Agent Standards Initiative in February 2026, explicitly calling out that AI agent systems "are capable of taking autonomous actions that impact real-world systems or environments, and may be susceptible to hijacking, backdoor attacks, and other exploits." When NIST is racing to build standards around agentic AI security, that tells you the threat isn't theoretical.
How AI Agents in OT Security Are Changing the Threat Landscape
Let me be specific about what's different. Traditional malware follows a script. It executes a predetermined sequence, and defenders can study that sequence to build signatures and detection rules. AI agents don't work that way.
Unlike programmable malware, AI agents can reason, adapt, and act within OT networks without continuous human direction (Cybersecurity Magazine). They're capable of automating and adapting each phase of an attack: reconnaissance, lateral movement, privilege escalation, and objective execution. Each step can be adjusted in real time based on what the agent discovers in your environment.
| Capability | Traditional Malware | AI Agents in OT Security Environments |
|---|---|---|
| Reconnaissance | High-volume scanning, easily detected | Low-noise, adaptive mapping of PLCs, RTUs, HMIs |
| Lateral Movement | Fixed exploit chains, predictable paths | Real-time path evaluation, protocol-aware pivoting |
| Adaptation | Static behavior, signature-matchable | Reinforcement learning, evades detection patterns |
| Speed | Human-directed or scripted timing | Machine-speed, minutes from access to objective |
| Process Targeting | Generic destruction or data theft | Maps control loops, targets physical process disruption |
AI Agent Attack Capabilities in Industrial Control Systems
Here's what that looks like in practice for an OT network:
- Autonomous reconnaissance: An AI agent can map network topology, identify PLCs, RTUs, and HMIs, and catalog communication protocols without generating the volume of traffic that traditional scanning tools produce. It learns the environment the way a patient, skilled human operator would, but at machine speed.
- Adaptive lateral movement: Instead of relying on a fixed exploit chain, the agent evaluates available pathways in real time. If one route is blocked, it pivots. If a particular protocol is in use (Modbus, EtherNet/IP, OPC UA), it adapts its approach accordingly.
- Process-aware targeting: The most concerning development is agents that can map control loops and understand physical process relationships. The Dragos 2026 OT Cybersecurity Report documented threat groups "progressing from reconnaissance to operational disruption," with adversaries actively mapping control loops and understanding how to manipulate physical processes.
SecurityWeek's Cyber Insights 2026 series captured the trajectory well: one expert predicts that by mid-2026, "at least one major global enterprise will fall to a breach caused or significantly advanced by a fully autonomous agentic AI system that uses reinforcement learning and multi-agent coordination to autonomously plan, adapt, and execute an entire attack lifecycle" (SecurityWeek).
That's not FUD. That's a sober assessment of where the technology is headed.
Why Detection-First Strategies Fall Short Against AI-Driven Attacks
I've had dozens of conversations with OT security leaders over the past year (including what our team heard at S4x26), and most have invested heavily in detection: network monitoring, anomaly detection, ICS-specific SIEM rules. That investment isn't wasted. Detection is necessary. But it's not sufficient against AI threats to industrial control systems.
Here's the thing. Detection assumes you can observe malicious behavior, classify it, and respond before the attacker achieves their objective. That assumption breaks down when the attacker operates at machine speed and adapts its behavior to avoid known detection patterns.
Consider the numbers. The SANS 2025 State of ICS/OT Security survey found that more than one in five organizations (21.5%) reported a cybersecurity incident in the past year, and four in 10 of those events caused operational disruption. Only 13% of organizations have fully implemented advanced controls such as session recording or ICS/OT-aware access. That gap between incident frequency and control maturity is exactly what AI agents will exploit. This is the core challenge of AI OT cybersecurity: the threat is evolving faster than the controls designed to contain it.
The SANS team has been clear on this point: "IT and ICS/OT are not the same, and standard IT actions such as dropping suspected traffic or default 'block' concepts are NOT recommended, with or without AI for ICS environments" (SANS ICS/OT Cybersecurity and AI Considerations). You can't just bolt IT security patterns onto OT and expect them to work. The safety and availability requirements are fundamentally different.
The uncomfortable truth is that detection without containment architecture is a monitoring exercise. You'll see the attack. You may even classify it correctly. But if an AI agent can move laterally across flat OT network segments faster than your team can respond, detection alone becomes an expensive way to document what you lost. This is why addressing AI agents in OT security requires rethinking architecture, not just adding more sensors. The agentic AI threat to OT is architectural in nature, and the response must be architectural too.
The Agent Deployment Problem: You Can't Install Software on a PLC
This is where the conversation gets uncomfortable for a lot of security vendors. The dominant approach in IT microsegmentation relies on software agents installed on endpoints. That works fine for Windows servers and Linux workstations. It doesn't work in OT.
PLCs don't run endpoint agents. RTUs don't accept software installations. Many HMIs run embedded or legacy operating systems that can't support additional software without risking process stability. Safety-instrumented systems (SIS) are explicitly designed to resist modification.
Our team talked to several CISOs at S4x26 who described the same frustration. They've been pitched agent-based microsegmentation solutions that sound compelling in the IT context but fall apart the moment they hit the plant floor. One security director from a major energy company told our team, "We evaluated three microsegmentation vendors last year. Every one required agents on endpoints. That's a non-starter for 70% of our OT assets."
The Dragos 2026 report reinforces why this matters. Ransomware attacks against industrial organizations rose 64% year over year, with 119 ransomware groups now targeting industrial sectors, up from 80 in 2024 (Dragos). Meanwhile, 12% of OT devices carry known exploitable vulnerabilities, and 7% are linked to active ransomware campaigns (SecurityWeek). These are devices that, in many cases, cannot be patched, cannot run agents, and cannot be taken offline for upgrades.
If your segmentation strategy requires software on the endpoint, you've already excluded the assets that need protection most.
Microsegmentation for OT Networks: The Architectural Defense Against AI Agents
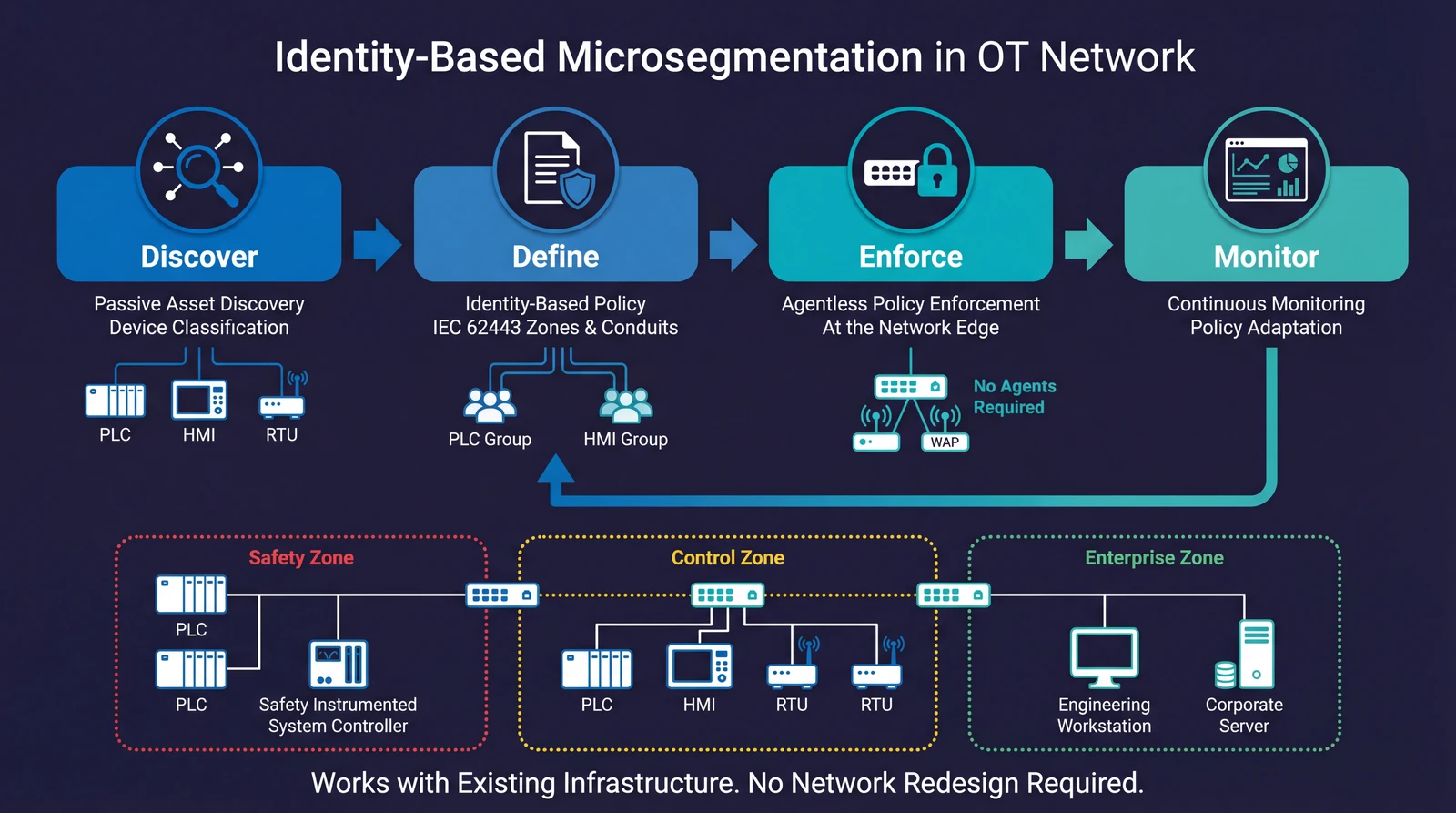
So what does work? In my experience, the answer lies in moving policy enforcement to the network layer itself, using identity-based microsegmentation that doesn't depend on endpoint agents. This is the Zero Trust approach applied to OT: verify every device identity, enforce least-privilege communication, and never assume trust based on network location.
The concept isn't new. IEC 62443 has defined the zones and conduits model for years, and it remains the gold standard for OT network architecture (IEC 62443 network segmentation requirements). What's changed is the technology available to implement it. Traditional approaches required manual VLAN configuration, complex firewall rule sets, and months (or years) of deployment. That operational burden is why so many OT environments still run essentially flat networks.
Modern identity-based approaches flip this model. Instead of defining policy by IP address, VLAN, or port number, you define policy based on what a device is: its function, its role in the process, its risk profile, its communication requirements. A PLC controlling a chemical batch process gets a different policy than an HMI displaying production metrics, regardless of which switch port either one is plugged into. This is what effective OT network segmentation looks like in practice.
This matters enormously for AI OT cybersecurity in 2026 because it addresses the core problem: blast radius containment. Even if an AI agent gains initial access to an OT network, identity-based microsegmentation limits what it can reach. The agent can't move laterally to a safety controller if the network enforces that the compromised asset has no communication path to that controller in the first place.
How to Implement OT Network Segmentation Against AI Threats
The approach that works in practice follows a discover-then-control pattern. I've seen it deployed in energy, manufacturing, and critical infrastructure environments, and the steps are consistent:
- Know what's on your network first: You can't protect what you can't see. Passive discovery identifies every device on the network, classifies it by type and function, and maps its communication patterns. This gives you the identity context needed to write meaningful policy.
- Policy definition based on identity and function: Using frameworks like IEC 62443 zones and conduits, you define which device types can communicate with which other device types, and over which protocols. ICS network segmentation comes to life in a software-defined way when policy maps to device identity rather than static network topology.
- Agentless enforcement at the network edge: Policy is enforced at the existing network infrastructure (switches, access points) without requiring agents on endpoints. This is what makes it viable for OT. The PLC doesn't need to know or care that policy is being enforced. The network handles it.
- Keep adjusting as the network changes: As new devices connect or communication patterns change, the system updates its understanding and can flag or automatically adjust policy. This is essential for environments where the "Connect" thesis is playing out in real time.
This is the approach we've built at Elisity: identity-based microsegmentation that deploys on existing switching infrastructure without requiring endpoint agents, firmware modifications, or network redesign.
Honest Limitations and Considerations
I want to be direct about what microsegmentation for OT networks does not solve. It's an architectural control, not a silver bullet.
It doesn't replace detection. You still need network monitoring, anomaly detection, and incident response capability. Microsegmentation reduces the blast radius and buys your team time. It doesn't eliminate the need to detect and respond to threats.
It requires asset visibility first. If you don't have a clear picture of what's on your network and how it communicates, you can't write effective policy. Many organizations discover during the asset inventory phase that their OT networks are far more complex than they assumed. That discovery process takes time and care, particularly in environments with legacy protocols and undocumented connections.
Policy design demands OT expertise. Writing microsegmentation policy for a manufacturing line is different from writing policy for an IT data center. You need people who understand the physical process, the control hierarchy, and the safety implications of restricting communication paths. Getting this wrong can disrupt production, and in safety-critical environments, the stakes are higher.
It doesn't address supply chain compromise directly. If a threat actor compromises a legitimate firmware update or vendor remote access session, they may operate within an allowed communication path. Microsegmentation limits the scope of what they can reach, but it doesn't detect compromise within a trusted channel. Defense in depth remains essential.
What Security Leaders Should Do Now
Based on what our team heard at S4x26 and what I've seen in real deployments, here's what I'd prioritize if I were running OT security for a critical infrastructure organization today.
- Get real about your asset inventory. The SANS 2025 survey found that 54% of organizations plan to invest heavily in asset inventory and visibility heading into 2026 and 2027. If you're not in that group, you should be. You cannot segment what you cannot see. Start with network asset discovery for microsegmentation. Map every device, every protocol, every communication flow. This is the foundation everything else builds on.
- Evaluate your segmentation architecture against agentic threats. Ask your team a specific question: if an AI agent compromised a single endpoint on our OT network today, how far could it move laterally before hitting a policy boundary? If the answer is "across the entire flat network," you have an architectural problem that no amount of detection tooling will solve. Stopping lateral movement requires architectural controls, not just monitoring.
- Adopt an identity-based, agentless approach for OT segmentation. Don't try to force IT segmentation models onto OT environments. Look for solutions that enforce policy at the network layer without requiring agents on endpoints. Elisity's identity-based microsegmentation platform does exactly this, using existing switching infrastructure as enforcement points. Align your segmentation design with IEC 62443 zones and conduits. The framework exists for a reason. The leading OT security vendors in 2026 are the ones building around this principle.
Building an AI-Ready OT Security Architecture
- Plan for the "Connect" reality with granular network controls. The business will keep connecting OT systems to enterprise platforms, cloud analytics, and AI-driven tools. Fighting that trend is a losing battle. Instead, build the architectural controls that let those connections happen safely. Identity-based microsegmentation gives you the ability to say yes to connectivity while maintaining granular control over what communicates with what. Specifically, map every new IT/OT integration point, define communication policies before the connection goes live, and monitor for anomalous cross-zone traffic from day one. Treating each new connection as a policy decision rather than a network plumbing exercise is how you stay ahead of AI agents targeting OT security gaps in converged environments.
- Test your architecture against AI-speed scenarios. Traditional tabletop exercises assume human-speed attacks. Start modeling scenarios where reconnaissance to lateral movement to objective happens in minutes, not days. Organizations that include operational staff in cybersecurity exercises report readiness levels 1.7 times higher than those that don't, according to the SANS 2025 survey. Bring your plant operators and control engineers into these exercises. They understand the process dependencies that your IT security team may not.
Looking Ahead: AI OT Cybersecurity in 2026 and Beyond
S4x26 made one thing clear: the OT security community is past the point of debating whether AI agents in OT security change the threat landscape. They do. The question now is whether our defensive architectures can adapt fast enough.
I'm cautiously optimistic. The tools and frameworks exist. IEC 62443 provides the architectural blueprint. Zero Trust network security principles provide the philosophy. Identity-based microsegmentation for agentic AI threats provides the enforcement mechanism that works in environments where endpoint agents can't. The NIST AI Agent Standards Initiative will bring much-needed rigor to how we think about securing autonomous systems.
But tools and frameworks are only useful if organizations act on them. The window between "emerging threat" and "active exploitation" is closing faster than it ever has. As AI agents grow more capable of targeting OT security infrastructure, organizations that wait for the first major AI-driven OT incident to start their segmentation journey are already behind.
The "Connect" theme at S4x26 wasn't a warning. It was a description of reality. The question is whether we connect securely or just connect.
Further reading:
- Understanding and Preventing Lateral Movement Attacks
- AI Agent Network Security: Why Microsegmentation Is the Missing Layer
- What Is Microsegmentation and How Does It Work?
- CISA Microsegmentation in Zero Trust
- How Claude AI Weaponized Lateral Movement
About the Author
Charlie Treadwell is CMO at Elisity and writes about OT security and AI agent threats from both sides: building with autonomous AI tools daily and working in cybersecurity. He is Elisity Platform Certified. The Elisity team was at S4x26 in conversations with CISOs and plant security leaders about agentic AI's impact on industrial control systems. Connect with Charlie on LinkedIn.
Frequently Asked Questions About AI Agents in OT Security
How can AI agents be used to attack industrial control systems?
AI agents can autonomously perform reconnaissance on OT networks, identifying PLCs, RTUs, HMIs, and their communication protocols without generating the high-traffic signatures that traditional scanning produces. Once inside, they adapt their lateral movement strategies in real time, pivoting between exploit paths based on what they discover. In practice, the most advanced agents can map control loops and understand physical process relationships, enabling targeted disruption of industrial operations. Unlike scripted malware, they use reinforcement learning to optimize their approach with each step, which is what makes them so much harder to detect and contain.
What are the best defenses against AI-driven threats to OT environments?
The most effective defense combines architectural controls with monitoring. Identity-based microsegmentation at the network layer limits blast radius by enforcing communication policies based on device identity and function, not network location. This is critical in OT because endpoint-based agents can't be installed on PLCs, RTUs, or safety systems. What I've seen work best starts with comprehensive asset discovery and classification as the visibility foundation, adds ICS-aware anomaly detection and network monitoring as a detection layer, and includes regular tabletop exercises modeled on machine-speed attack scenarios. No single technology is sufficient; defense in depth remains the guiding principle.
How does microsegmentation for OT networks defend against AI-powered attacks on ICS?
In short, microsegmentation creates granular policy boundaries that restrict which devices can talk to which other devices, and over which protocols. When an AI agent gains initial access to an OT network, those boundaries prevent it from moving laterally to critical assets like safety controllers, SCADA servers, or engineering workstations. Identity-based approaches define these boundaries based on what a device is (its function and role) rather than where it sits on the network, This is ICS network segmentation aligned with the IEC 62443 zones and conduits model, implemented through identity rather than static VLANs. The enforcement happens at the network switch layer without requiring software agents on OT endpoints, which is what makes it viable for environments with legacy and embedded devices.
What did S4x26 reveal about the future of AI in OT security?
S4x26's "Connect" theme highlighted what most practitioners already feel: the next one to three years will bring a massive wave of AI-driven connections between OT systems, enterprise platforms, and analytics tools. The Proof of Concept Pavilion demonstrated that security product interoperability with real industrial automation systems (Siemens and Rockwell Automation) isn't aspirational anymore; it's a baseline expectation. The key takeaways were clear: detection-first strategies alone aren't enough against machine-speed attacks, agentless enforcement is necessary for OT environments, and IEC 62443 zones and conduits provides the right architectural model for AI-era defense. The industry has to move from perimeter-based thinking to identity-based, granular network controls.
Share this
- May 2026 (5)
- April 2026 (10)
- March 2026 (6)
- February 2026 (14)
- January 2026 (4)
- December 2025 (4)
- November 2025 (2)
- October 2025 (5)
- September 2025 (4)
- August 2025 (5)
- July 2025 (5)
- June 2025 (5)
- May 2025 (4)
- April 2025 (5)
- March 2025 (6)
- February 2025 (3)
- January 2025 (5)
- December 2024 (4)
- November 2024 (5)
- October 2024 (7)
- September 2024 (5)
- August 2024 (3)
- July 2024 (4)
- June 2024 (2)
- April 2024 (3)
- March 2024 (2)
- February 2024 (1)
- January 2024 (3)
- December 2023 (1)
- November 2023 (1)
- October 2023 (2)
- September 2023 (3)
- June 2023 (1)
- May 2023 (3)
- April 2023 (1)
- March 2023 (6)
- February 2023 (4)
- January 2023 (3)
- December 2022 (7)
- November 2022 (3)
- October 2022 (1)
- July 2022 (1)
- May 2022 (1)
- February 2022 (1)
- November 2021 (1)
- August 2021 (1)
- May 2021 (2)
- April 2021 (2)
- March 2021 (3)
- February 2021 (1)
- November 2020 (2)
- October 2020 (1)
- September 2020 (1)
- August 2020 (3)

.png)


No Comments Yet
Let us know what you think