Share this
Healthcare Microsegmentation: How SIH Secured 400+ Beds
by Mick Coady on Feb 25, 2026 5:34:36 PM
Every CISO I talk with in healthcare gets it immediately: your network is full of devices that can't protect themselves. Infusion pumps, bedside monitors, imaging systems, pneumatic tube controllers. These devices were built to deliver patient care, not to defend against ransomware. And the number keeps growing. The average hospital now connects thousands of IoMT devices, most running outdated operating systems, many without the capacity for endpoint agents or antivirus.
The standard advice is simple: segment your network. Isolate the vulnerable from the critical. Contain lateral movement before an attacker can pivot from a compromised device to your patient records, your imaging archive, or your clinical applications.
Here's where it breaks down. Traditional segmentation approaches ask you to redesign your network, deploy agents on every endpoint, or staff a team of engineers to manage a NAC platform. For a regional healthcare system running on a constrained budget with limited cybersecurity staff, those options aren't options at all. They're architecture fiction.
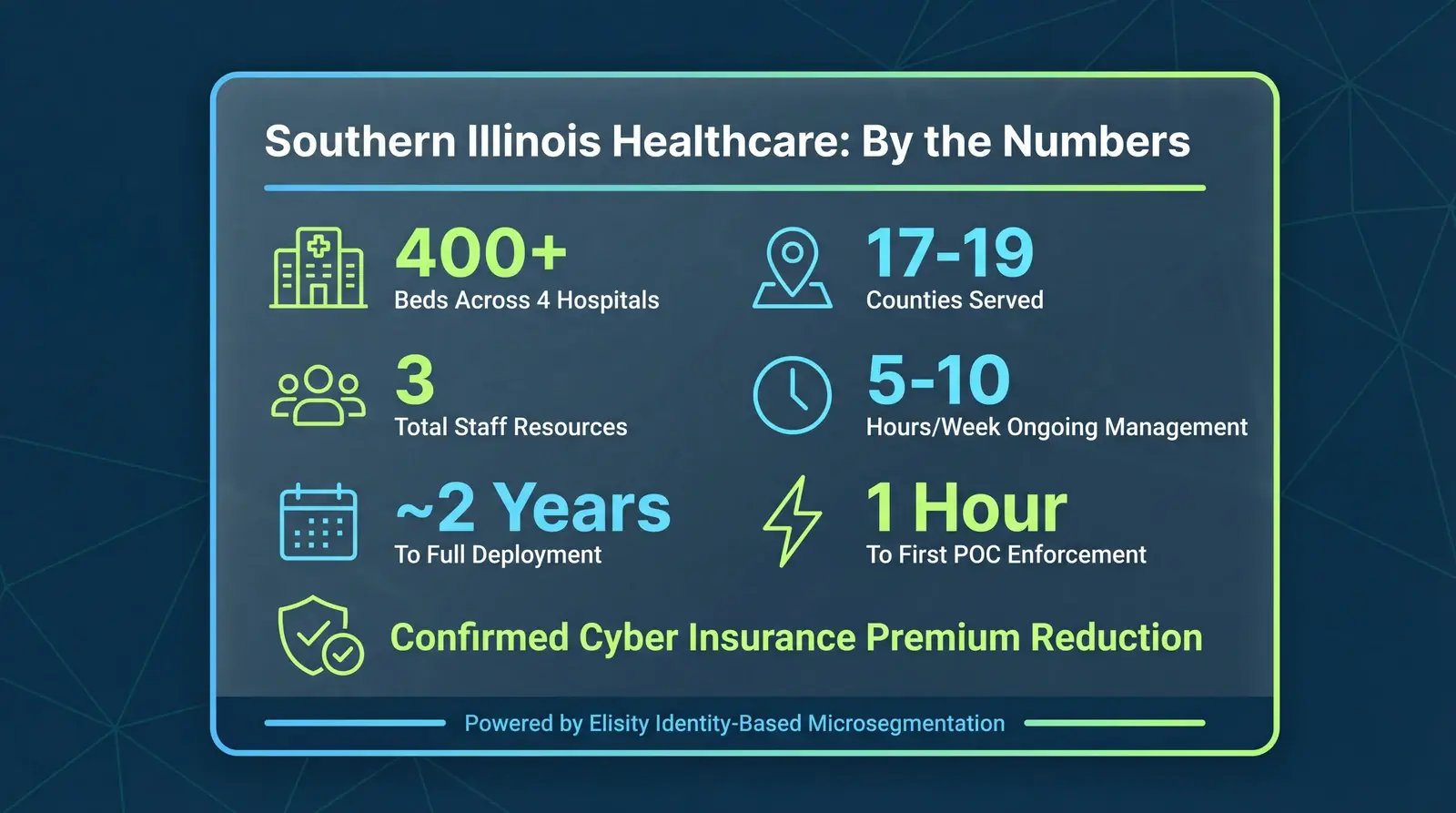
That's why when I sat down with Taylor Calloni at CHIME ViVE 2026 in Los Angeles (where I also wrote about broader conference themes), his story resonated so deeply. Taylor is a Cybersecurity Engineer III at Southern Illinois Healthcare (SIH), a not-for-profit system operating four hospitals, roughly 400 beds, and a Level II trauma center serving 17 to 19 counties across southern Illinois. He took SIH from zero microsegmentation to full wired-network segmentation with three total resources. Not thirty. Three.
What follows isn't a chronological recap. It's a healthcare microsegmentation playbook built from seven replicable patterns that any organization can study, adapt, and apply. Taylor is the practitioner who proved these patterns work. I'm just the one who's seen enough deployments across industries to recognize why they matter.

Pattern 1: Why Traditional Healthcare Microsegmentation Approaches Fail
Before I break down what SIH did right, it's worth understanding what every healthcare security team runs into when they try to segment their network. I've watched organizations start segmentation projects and abandon them halfway through. I've seen facilities choose no segmentation over disruptive segmentation. The failure modes are the same three every time.
The first constraint is device compatibility. Many medical and IoMT devices cannot run endpoint agents. They're FDA-regulated, running embedded or legacy operating systems, and any software modification risks voiding compliance or warranty. Agent-based microsegmentation solutions simply do not work for the devices that need protection most.
The second constraint is budget. Network redesigns cost millions. NAC platforms require dedicated staff to operate. For a regional system like SIH, these approaches are financially out of reach.
The third constraint is operational risk. You cannot tolerate downtime in a facility that runs trauma services around the clock. Every change carries the risk of disrupting clinical workflows, disconnecting a bedside monitor, or interfering with data flowing between a medical device and its server.
Taylor put it plainly during our conversation:
"No one's got the money for a network redesign. No one's got the funds or the resources. And a lot of these medical devices can't take agents."
— Taylor Calloni, Cybersecurity Engineer III, Southern Illinois Healthcare
He went further, describing SIH as "a regional healthcare facility that's strapped on a budget," a Level II trauma center with 400 beds serving communities from the Mississippi River to the Ohio River. "We can't have downtime," he said plainly.
I see this pattern repeated across healthcare: the devices that need segmentation most are the ones that traditional tools can't reach. The organizations that need segmentation most are the ones that can't afford the complexity. Any viable microsegmentation approach for healthcare has to solve for all three constraints simultaneously.
Pattern 2: Visibility as the Foundation for Healthcare Network Segmentation
You can't segment what you can't see. I've said this to hundreds of security leaders, and while the phrase risks being overused, the problem behind it remains unsolved in most healthcare environments. The reality is that many hospitals still rely on manually maintained IPAM spreadsheets, partial endpoint agent coverage, and institutional memory to track their connected assets.
At SIH, Taylor described exactly this gap:
"You deploy AD agents, endpoint agents, stuff gets missed or excluded, and then you don't know where that device is, what it's connected to. It's touching a switch somewhere, but you don't know which one. And if it's in a spreadsheet somewhere or written on a notepad."
— Calloni
This is where the work gets real. SIH needed a source of truth for their asset environment, one that didn't depend on agents reaching every device or a human keeping a spreadsheet current. Their approach was to combine multiple data sources into a unified view: their Claroty Medigate solution for IoMT device identification, CrowdStrike EDR for managed endpoints, IPAM for IP and MAC address data, and network flow data from the switches themselves.
The key insight here is data enrichment through integration. No single tool sees everything. An IoMT security platform identifies medical device types and clinical context. An EDR platform covers managed IT assets. Network flow data reveals what's actually communicating with what at the switch port level, regardless of whether a device has an agent. When you layer these together, you move from "we think we have about 2,000 medical devices" to a verified, continuously updated inventory that shows every device, its identity, its location, and its communication patterns.
This pattern applies far beyond SIH. Every healthcare organization I work with that succeeds at segmentation starts with this step. Not with policy writing. Not with VLAN redesign. With building a source of truth they can actually trust.
Pattern 3: Simulation Before Enforcement in Clinical Environments
Here's a pattern that separates successful hospital microsegmentation deployments from the ones that get rolled back on day two: simulation before enforcement.
In a clinical environment, the cost of a false positive is measured in patient care disruption. Block the wrong communication path between a bedside monitor and its central station, and a nurse loses visibility into patient vitals. Interrupt data flow from an infusion pump to the pharmacy system, and medication delivery stalls. These aren't theoretical risks. I've seen them happen at organizations that moved too quickly from visibility to enforcement.
SIH took a disciplined approach. After building their asset visibility foundation, they placed segmentation policies into simulation mode, monitoring what would happen if enforcement were active without actually blocking traffic. This allowed Taylor and his team to validate that policies wouldn't disrupt clinical workflows before flipping the switch.
"We were able to put policies in simulation mode to monitor the activity, to make sure we're not going to disrupt patient data, we're not going to take that device offline."
— Calloni
I recommend this approach to every organization, not just healthcare. But in healthcare, it's non-negotiable. Simulation mode transforms segmentation from a high-stakes, all-or-nothing deployment into a measured, evidence-based rollout. You see the data. You validate the behavior. You enforce with confidence. The blast radius of a misconfigured policy in simulation is zero.
Pattern 4: Sequenced Deployment from Low-Risk to High-Complexity
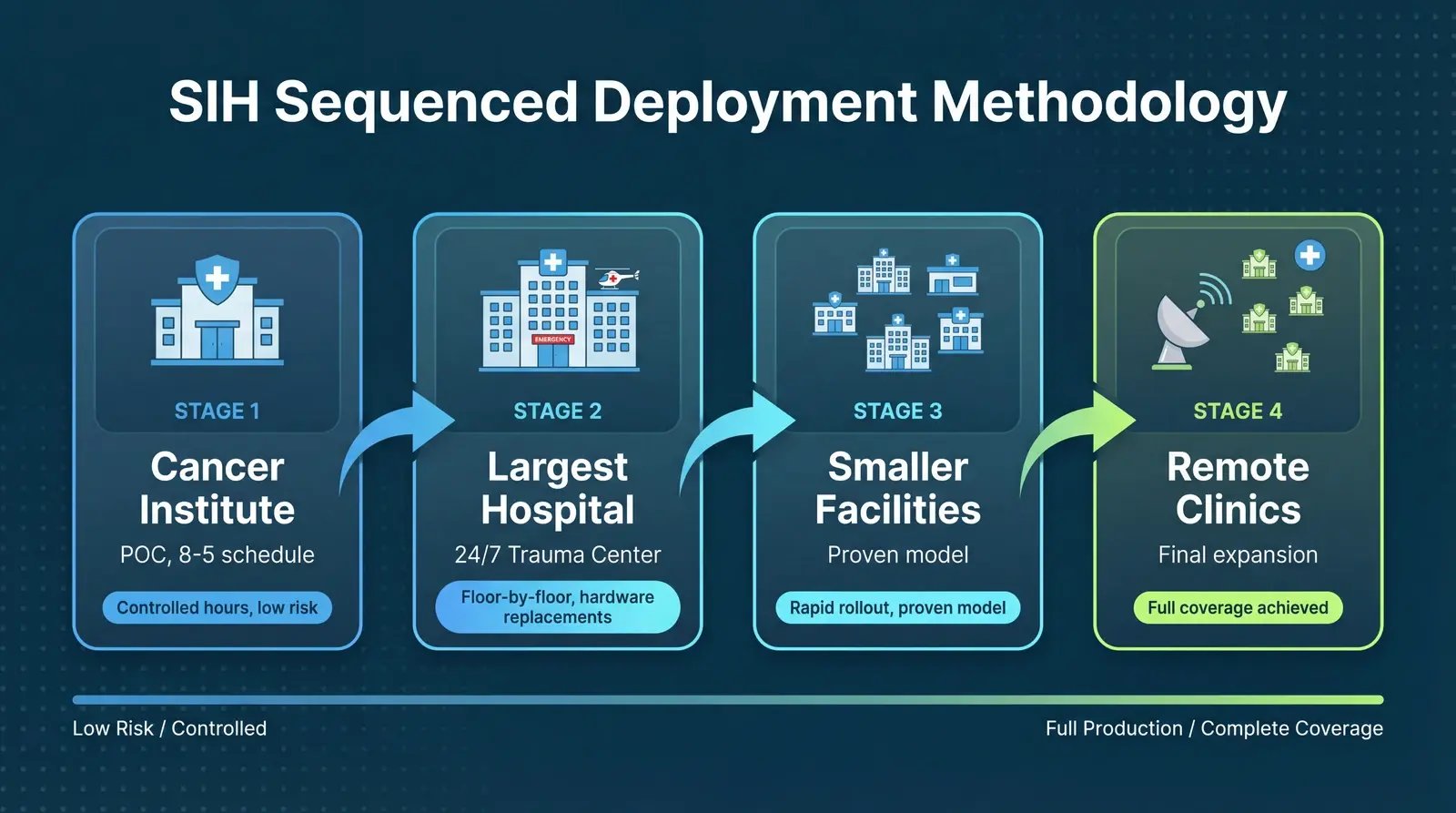
One of the most instructive aspects of SIH's approach was how Taylor and his team sequenced their deployment. They didn't try to segment the entire system at once. They chose a deliberate path from lower-risk environments to higher-complexity ones, building operational confidence at each stage.
"For the POC, we started at our Cancer Institute. That's only eight to five, so we were able to go in after hours, deploy, create, and fix. After that, we started at our biggest site, dwindled down to the smallest, then branched out to all the remote clinics."
— Calloni
The logic is elegant. The Cancer Institute operates on a predictable daytime schedule, which meant Taylor's team could deploy after hours, test, adjust, and resolve any issues without clinical pressure. This environment served as a controlled proving ground. And what happened during that proof of concept set the tone for everything that followed:
"Within an hour it was deployed on a switch, monitoring and blocking. And it was like, this isn't real."
— Calloni
I've been in this industry long enough to know that skepticism is healthy. Taylor had it too. As he expanded beyond the Cancer Institute, he kept waiting for the other shoe to drop: "I kept waiting for the moment where something's got to break, something's got to give. And it just didn't. It just worked."
Once they validated the approach at the Cancer Institute, they moved to SIH's largest hospital, then progressively smaller facilities, then outpatient clinics. At the main hospital (the 400-bed, 24/7 trauma center) the team went floor by floor. Some floors required switch hardware replacements, which the two-person network team coordinated during scheduled maintenance windows. Once the hardware was in place, the segmentation platform deployed onto the switches and began monitoring and discovering devices.
This sequencing pattern, start small, prove the model, scale with confidence, is something I've seen work across industries. In manufacturing, teams often start with a single production line. In financial services, it might be a branch office. The principle is the same: reduce variables, learn, then expand. SIH executed it with discipline.
Pattern 5: Operational Sustainability with Minimal Resources
Deployment is one thing. Sustaining a microsegmentation program over time is another. I've seen organizations deploy segmentation successfully only to watch it atrophy because the operational burden exceeded what their team could maintain. Policies drift. New devices appear without coverage. The segmentation platform becomes another tool that "someone used to manage."
This is where SIH's story becomes particularly compelling for resource-constrained healthcare organizations. Taylor was clear about the numbers: three total resources handled the entire deployment. Two network engineers managed the switch infrastructure work across all sites. Taylor, as the security administrator, managed the policy creation, simulation, and enforcement.
"Since it's been deployed, it's almost hands-off. I'm in it maybe five to ten hours a week, just doing granular changes or granular policy enforcement. It's very low overhead."
— Calloni
Five to ten hours per week. For full wired-network microsegmentation across four hospitals, multiple clinics, and hundreds of beds. That's the difference between a segmentation approach that works on a slide deck and one that works in a real healthcare environment with real staffing constraints.
The deployment phase required significant focused effort from Taylor as the team rolled out site by site. Microsegmentation is not a weekend project. But the post-deployment operational model, a single engineer spending a fraction of their week on ongoing policy management, is sustainable even for small security teams. And it frees the rest of the team to focus on other priorities rather than perpetually managing network access controls. That kind of operational efficiency is what separates a platform-driven approach from a point-product patchwork.
Pattern 6: Unexpected Wins and the Shift from "No" to Enablement
Every deployment surfaces surprises. In my experience, the most valuable ones are the things you didn't know you didn't know. At SIH, the visibility that came with microsegmentation revealed shadow IT that had been invisible to every previous tool.
"We found our hospitals have a couple tube systems. There were local, non-domain-bound Windows 7 machines plugged into the jack, internet-capable. There's no spreadsheet, no documentation of this device. Why is it here?"
— Calloni
Internet-capable Windows 7 machines, undocumented, unmanaged, connected to the hospital network and supporting pneumatic tube systems. No endpoint agent knew about them. No spreadsheet tracked them. No vulnerability scanner could assess what it couldn't find. This is the kind of discovery that makes a CISO's stomach drop, and it's exactly the kind of hidden risk that network-level visibility exposes.
But the unexpected benefit that stood out to me most was the cultural shift Taylor described. Before microsegmentation, the security team's default answer to new device requests was "no." A vendor needs temporary network access to archive data from an aging imaging system? No, the exclusion policy prevents it. A clinical department wants to connect a new device type? No, we can't secure it.
With granular, identity-based segmentation in place, that answer changed:
"It's changing the rigid security rules of 'no, you can't do that, we have an exclusion policy, you're not putting that on the network' to 'yeah, I can help you with that.'"
— Calloni
When a vendor needs temporary access, Taylor can add the device's MAC address, apply a controlled, time-bounded policy, let the vendor do their work, and pull it right back off the network. The security team becomes an enabler instead of a blocker. This is a pattern I see across every successful segmentation deployment, and it matters enormously for the relationship between security and clinical operations.
Pattern 7: Business Impact Beyond Security
Technical outcomes matter to security teams. Business outcomes matter to leadership and boards. SIH's microsegmentation deployment delivered both.
The most tangible business driver was cyber insurance. Taylor was direct about the catalyst that accelerated SIH's segmentation initiative:
"Our cyber insurance issuer was keen to let us know, 'Hey, you've got to have something for segmentation. You can't just tell me you've got a guest network and a broad network.'"
— Calloni
This tracks with what I'm seeing industry-wide. According to Akamai's 2025 Segmentation Impact Study of 1,200 security leaders, 60 percent of surveyed organizations reported receiving premium reductions after improving their segmentation posture, and 75 percent of insurers now assess segmentation maturity during underwriting. SIH confirmed that their deployment contributed to a reduction in their cyber insurance premium.
A leadership change at SIH also played a role, bringing increased focus on security that helped free budget for the initiative. This is an important contextual factor. Even the best technical solution needs organizational alignment and executive support to move forward.
Healthcare organizations also face increasing regulatory pressure. The HHS 405(d) Cybersecurity Performance Goals include network segmentation as an "enhanced" goal, and HHS has signaled its intention to move toward enforceable cybersecurity standards informed by these goals. With healthcare remaining the most targeted sector for ransomware (a 49 percent year-over-year increase in disclosed attacks in 2025, according to the HIPAA Journal), and the average healthcare breach costing $10.93 million according to IBM's 2025 Cost of a Data Breach Report, the case for microsegmentation extends well beyond insurance premiums.
SIH Microsegmentation: By the Numbers
- 400+ hospital beds across four facilities
- 17 to 19 counties served across southern Illinois
- 3 total resources for full microsegmentation deployment
- 5 to 10 hours per week for ongoing policy management
- Phased rollout from POC to full wired-network coverage, site by site
- 1 hour from deployment to monitoring and blocking in the initial POC
- Confirmed cyber insurance premium reduction post-deployment
Those numbers tell a story of what's possible when the approach matches the constraints. But the numbers alone don't capture the full picture.
What This Means for Your Organization
I want to be honest about what SIH's experience tells us and what it doesn't. Taylor's success was real, and the patterns are replicable, but context matters. SIH had a leadership change that prioritized security. They had an insurance carrier applying pressure. Taylor himself brought the dedication to make it his primary focus throughout the rollout. Not every organization has all of these factors aligned.
The deployment also focused on wired-network segmentation. SIH's wireless network already had ACL-based controls (though not microsegmentation), and Taylor noted that conversations about extending platform-managed segmentation to wireless are just beginning. Full environment coverage remains a continuing effort, not a completed project.
What is universally transferable are the patterns themselves. Start with visibility. Enrich data from multiple sources. Simulate before you enforce. Sequence your deployment from lower-risk to higher-complexity. Design for operational sustainability from day one. And expect to discover things about your network you didn't know.
When I asked Taylor what advice he'd give his peers, he cut through the complexity with practitioner clarity:
"Microsegmentation is a scary word in security and networking. But it's doable. You just set it up, knock it down, build a program to get through it."
— Calloni
I've spent nearly 30 years in this industry, working across healthcare, manufacturing, financial services, and critical infrastructure. The pattern I see at the organizations that succeed is consistent. They don't wait for perfect conditions. They find an approach that works within their constraints, prove it in a controlled environment, and scale methodically.
Taylor Calloni did exactly that. From a small town in southern Illinois, with three resources, a constrained budget, and a network full of devices that can't protect themselves, he built a microsegmentation program that serves as a model for any healthcare organization willing to start.
The devices can't protect themselves. Your network can.
Frequently Asked Questions About Healthcare Microsegmentation
How do you secure medical devices that can't run endpoint agents?
Medical devices, particularly FDA-regulated equipment and legacy systems, often cannot support endpoint agents or antivirus software. The answer is network-level microsegmentation that operates at the switch layer rather than on the device itself. This approach identifies devices through network flow data, MAC addresses, and integrations with IoMT security platforms, then enforces access policies based on device identity without requiring any software on the device. At SIH, this agentless approach was essential because, as Taylor Calloni noted, "a lot of these medical devices can't take agents." By segmenting at the network edge, you can isolate vulnerable devices to communicate only with their required clinical systems, limiting lateral movement even if the device itself is compromised.
How long does it take to implement microsegmentation in a hospital?
Implementation timelines vary based on the size of the environment, the number of sites, and whether switch hardware replacements are needed. SIH achieved full wired-network microsegmentation across four hospitals and multiple remote clinics through a phased rollout, with the initial proof of concept deploying in under an hour. The key accelerator is the deployment methodology: SIH started at a single site (their Cancer Institute), proved the model in a controlled environment, then expanded site by site from largest to smallest. Organizations with fewer sites or newer network infrastructure may complete faster. The critical factor isn't calendar time; it's using simulation mode to validate policies and sequencing deployment to build confidence without disrupting clinical operations.
Can microsegmentation help reduce cyber insurance premiums?
Yes. Cyber insurance carriers increasingly assess network segmentation maturity during underwriting, and organizations with demonstrated microsegmentation capabilities report premium reductions. At SIH, their insurance provider was explicit that "you've got to have something for segmentation. You can't just tell me you've got a guest network and a broad network." After deploying microsegmentation, SIH confirmed a reduction in their cyber insurance premium. According to Akamai's 2025 Segmentation Impact Study of 1,200 security leaders, 60 percent of surveyed organizations reported receiving premium reductions after improving their segmentation posture, and 75 percent of insurers now evaluate segmentation maturity as part of their underwriting process. Beyond premiums, microsegmentation provides the documentation and controls that strengthen claims approval and simplify audit reporting.
What is the role of asset visibility in healthcare network segmentation?
Asset visibility is the prerequisite for effective healthcare network segmentation. You cannot write accurate segmentation policies for devices you don't know exist, don't know the location of, or don't understand the communication patterns of. At SIH, the team discovered that their existing tools (AD agents, endpoint agents, manual IPAM spreadsheets) left significant gaps, with devices connected to switches that no inventory tracked. Their approach combined multiple data sources: an IoMT security platform for medical device identification, EDR for managed endpoints, IPAM for addressing data, and network flow analysis from the switches themselves. This multi-source enrichment created a continuously updated source of truth that revealed not only known devices but also shadow IT (such as undocumented Windows 7 machines supporting pneumatic tube systems). Without this visibility foundation, segmentation policies are based on assumptions rather than evidence.
What is IoMT security and why does it matter for hospitals?
IoMT (Internet of Medical Things) refers to the network-connected medical devices and clinical systems that modern hospitals depend on: infusion pumps, patient monitors, imaging systems, surgical robots, smart beds, and hundreds of other device types that generate, transmit, or act on clinical data. These devices are uniquely vulnerable for several reasons. Most run embedded or legacy operating systems that cannot be patched on a normal cadence. Many are FDA-regulated, meaning any software modification (including installing a security agent) risks voiding compliance or warranty. And their lifecycle often spans a decade or more, far outlasting the security assumptions built into their original design. Traditional IT security tools simply cannot reach them. That is why agentless, network-level microsegmentation has become a critical control for hospital security teams. By enforcing identity-based access policies at the switch layer, hospitals can isolate each IoMT device to only its required communication paths, containing lateral movement without touching the device itself. At SIH, this agentless approach was the only viable path to securing hundreds of medical devices across four facilities.
About the Author
Mick Coady is the Field CTO at Elisity, where he works with healthcare, manufacturing, and critical infrastructure organizations on identity-based microsegmentation strategy. With nearly 30 years in cybersecurity, including leadership roles at PwC, Deloitte, KPMG, and CA Technologies, Mick brings cross-industry practitioner experience to every engagement. He is a regular speaker at CHIME ViVE, HIMSS, and other healthcare technology conferences.
Related Reading:
Share this
- June 2026 (1)
- May 2026 (5)
- April 2026 (10)
- March 2026 (6)
- February 2026 (14)
- January 2026 (4)
- December 2025 (4)
- November 2025 (2)
- October 2025 (5)
- September 2025 (4)
- August 2025 (5)
- July 2025 (5)
- June 2025 (5)
- May 2025 (4)
- April 2025 (5)
- March 2025 (6)
- February 2025 (3)
- January 2025 (5)
- December 2024 (4)
- November 2024 (5)
- October 2024 (7)
- September 2024 (5)
- August 2024 (3)
- July 2024 (4)
- June 2024 (2)
- April 2024 (3)
- March 2024 (2)
- February 2024 (1)
- January 2024 (3)
- December 2023 (1)
- November 2023 (1)
- October 2023 (2)
- September 2023 (3)
- June 2023 (1)
- May 2023 (3)
- April 2023 (1)
- March 2023 (6)
- February 2023 (4)
- January 2023 (3)
- December 2022 (7)
- November 2022 (3)
- October 2022 (1)
- July 2022 (1)
- May 2022 (1)
- February 2022 (1)
- November 2021 (1)
- August 2021 (1)
- May 2021 (2)
- April 2021 (2)
- March 2021 (3)
- February 2021 (1)
- November 2020 (2)
- October 2020 (1)
- September 2020 (1)
- August 2020 (3)

.png)


No Comments Yet
Let us know what you think